People often use cybersecurity and information security like they mean the same thing. They don’t. Cybersecurity protects digital systems and online data, while information security protects information in every form, including digital files, paper records, and even private conversations.
That sounds like a small wording issue, but it isn’t. When teams confuse the two, they often buy the wrong tools, miss basic policies, and leave obvious gaps behind. The clearest way to see the difference is to start with what each one protects.
What cybersecurity and information security actually mean
Cybersecurity is about defending connected technology. That includes laptops, phones, servers, cloud apps, email systems, databases, and networks. If the threat comes through a screen, a device, or the internet, cybersecurity is usually involved.
Information security is broader. It protects the information itself, no matter where it lives or how people handle it. That could mean a customer file in a cloud drive, a printed contract in a drawer, or sensitive business plans discussed in a meeting room.
Easy line to remember: All cybersecurity is information security, but not all information security is cybersecurity.
Cybersecurity focuses on digital threats and connected systems
Think of cybersecurity as the front line for digital attacks. It deals with phishing emails, malware, ransomware, stolen passwords, account takeovers, and attempts to break into systems. It also covers patching software, monitoring suspicious activity, and locking down cloud settings.
For example, if an attacker tries to log in to your payroll app from another country, that’s a cybersecurity issue. If ransomware encrypts a company server, that’s cybersecurity too. The same goes for fake login pages, weak Wi-Fi protection, and exposed databases.
Because the term gets used loosely, many readers find it helpful to see a plain-English comparison like Coursera’s comparison of the two fields. The main point stays the same: cybersecurity protects digital assets from cyber threats.
Information security protects information in any form
Information security takes a wider view. Its job is to keep important information safe whether it’s stored, printed, spoken, mailed, or shared in person. That means it covers digital records, paper files, trade secrets, HR forms, financial reports, legal documents, and confidential conversations.
Picture a hospital. Protecting patient data in an online portal is part of information security. So is locking paper charts, restricting who can hear a case discussion, and setting rules for when old records must be destroyed.
In other words, information security is less about the device and more about the information itself. If the data matters, information security cares about it.
The biggest differences come down to scope, goals, and tools
The simplest way to compare them is side by side.
| Area | Cybersecurity | Information Security |
|---|---|---|
| Scope | Digital systems and online data | All information, digital, physical, and verbal |
| Main focus | Stopping and responding to cyber attacks | Reducing risk to information in any form |
| Common threats | Phishing, malware, hacking, ransomware | Theft, misuse, bad policies, human error, cyber threats |
| Typical controls | Firewalls, MFA, antivirus, monitoring | Access rules, badges, retention policies, training, secure disposal |
The takeaway is simple: cybersecurity is part of the bigger information security picture.
Cybersecurity is narrower, information security is broader
Cybersecurity only covers digital assets. Information security covers digital assets, physical records, and the rules around them.
A quick example makes this easy. Protecting a customer database from hackers is cybersecurity. Locking signed paper contracts in a cabinet is information security. Writing rules for who may access either one also falls under information security.
That broader scope is why many security leaders use information security when they talk about company-wide protection, not only online threats.
Cybersecurity is threat-focused, information security is risk-focused
Cybersecurity often works at attack speed. Teams watch for break-ins, block malicious traffic, patch weak systems, and respond when something goes wrong. The focus is immediate defense.
Information security still cares about attacks, but it also looks at the bigger risk picture. That includes policy, governance, compliance, data handling, vendor rules, and who gets access to what. A strong summary appears in IT Governance’s explanation of their shared goal, which ties both fields back to protecting information properly.
They use different controls, but both support the same goal
Cybersecurity controls are technical. Think firewalls, endpoint protection, intrusion detection, patching, multifactor authentication, and event monitoring.
Information security controls can be technical too, but many are administrative or physical. Think badge access, clean-desk rules, data retention schedules, approval steps for sharing files, staff training, and secure shredding.
Different tools, same mission: keep important information out of the wrong hands and available to the right people.
Real-world examples make the difference easier to see
Definitions help, but examples make the line clearer. In daily work, the two fields often show up side by side.
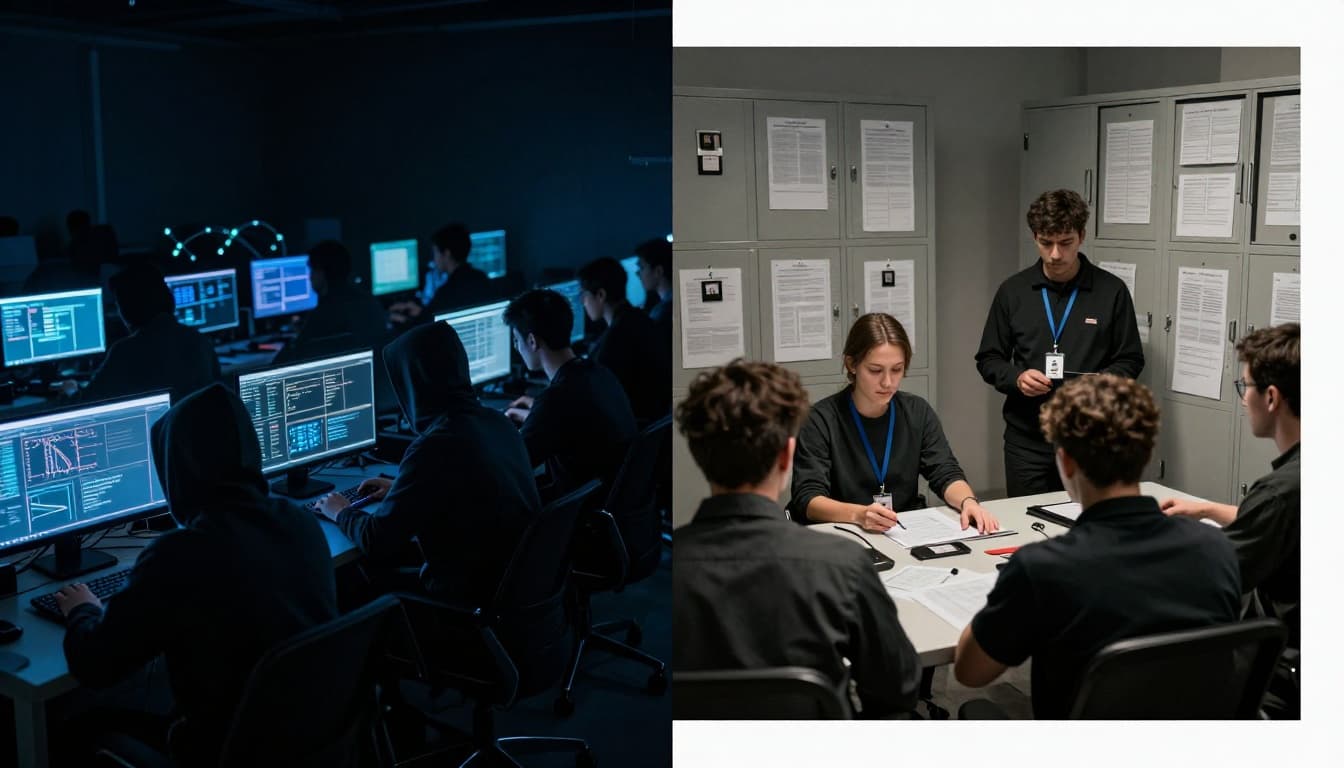
Examples of cybersecurity in action
A mail filter blocks a phishing message before an employee opens it. A security team patches a server after a new flaw appears. Monitoring software flags repeated failed logins from an unknown location. An admin tightens cloud app settings so outsiders can’t access stored files. After ransomware hits one device, the team isolates it to stop the spread.
Those are cybersecurity actions because they deal with digital systems, networked devices, and online threats.

Examples of information security in action
Now switch the scene. HR limits payroll access to a small group. Old employee records get shredded on schedule. A company writes rules for how teams may share customer data with vendors. Executives protect trade secrets with non-disclosure agreements and access limits. Managers train staff not to discuss private client details in public spaces.
None of those actions require a hacker to be present. Still, they’re all information security because they protect sensitive information from loss, misuse, or exposure.
That’s where the confusion often fades. If the problem is only digital, think cybersecurity first. If the problem is about information in any form, think information security.
What cybersecurity and information security have in common
Although the scope is different, the overlap is real. Both fields want the same three outcomes: information should stay private, stay accurate, and stay available when needed. Security teams often call this the CIA triad.

Both aim to keep information private, accurate, and available
Confidentiality means only approved people can see the data. A payroll file, for example, should not be open to the whole company.
Integrity means the data stays correct and untampered. A customer address or medical record must not be altered by mistake or by an attacker.
Availability means the right people can access the data when they need it. If a hospital system is down, care suffers fast.
If you want a simple outside reference, Splunk’s CIA triad explainer breaks down those three ideas well. Both cybersecurity and information security work toward them, even if the methods differ.
Both depend on smart policies, training, and regular review
Tools alone won’t solve this. A firewall can’t stop someone from printing a confidential report and leaving it in a lobby. At the same time, a locked file cabinet won’t stop a stolen password.
That’s why both fields depend on people, process, and technology working together. Teams need clear access rules, regular audits, incident response plans, and employee training that fits real work. Most breaches still involve human mistakes somewhere along the way, so awareness matters as much as software.
Which term should you use, and which one does your business need?
Use the term that matches the problem. Say cybersecurity when you mean online attacks, system hardening, endpoint protection, cloud defense, or incident response. Say information security when you mean the full protection picture, including policy, compliance, physical records, and employee behavior.
Use cybersecurity when talking about online attacks and system defense
If the conversation is about hackers, phishing, malware, networks, or suspicious logins, cybersecurity is the better term. It fits technical defense work and the teams that do it every day.
That choice matters because breach numbers remain huge. Recent US reporting shows about 1.35 billion victim notifications in 2024, driven by several massive events, while 2025 hit a record 3,322 reported breaches. A widely cited overview in DataFeature’s 2026 breach statistics roundup reflects the same trend: attacks keep coming, even when total records exposed swing year to year.
Use information security when talking about the full protection picture
Use information security when you’re discussing retention rules, physical records, privacy practices, access approvals, vendor handling, or company-wide risk management. It’s the better label when the goal is to protect information wherever it exists.
Most organizations need both. They need technical defenses against cyber attacks, and they also need rules for how people collect, share, store, and destroy information. One without the other is like locking your front door while leaving the filing cabinet open.
A good security strategy uses the right word, but more importantly, it covers the right risks. Cybersecurity protects digital systems from cyber threats. Information security protects all information, in every form.
If you want a practical next step, map where your sensitive information lives today. Then ask a simple question: are you protecting the system, the information, or both?
